Call Us (877) 740-5028
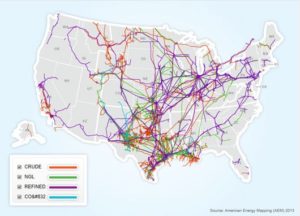 The US consumed 390M gallons of gasoline per day and 197M gallons of aviation fuel per day in 2019. As of 2020, 6.63 billion barrels of petroleum were consumed in the U.S. annually. Today, without oil, the U.S. doesn’t operate and that’s why the Energy Sector is one of 16 U.S. Critical Infrastructures. These figures come from the U.S. Energy Information Administration (EIA) and Cybersecurity & Infrastructure Security Agency (CISA.) The numbers also represent a jolting backdrop to the potential impact of the recent Colonial Pipeline hack. This is especially the case when you consider Colonial represents only about 5,500 miles of the ~2.6 million miles of US pipelines. (Diagram above from American Petroleum Institute. API)
The US consumed 390M gallons of gasoline per day and 197M gallons of aviation fuel per day in 2019. As of 2020, 6.63 billion barrels of petroleum were consumed in the U.S. annually. Today, without oil, the U.S. doesn’t operate and that’s why the Energy Sector is one of 16 U.S. Critical Infrastructures. These figures come from the U.S. Energy Information Administration (EIA) and Cybersecurity & Infrastructure Security Agency (CISA.) The numbers also represent a jolting backdrop to the potential impact of the recent Colonial Pipeline hack. This is especially the case when you consider Colonial represents only about 5,500 miles of the ~2.6 million miles of US pipelines. (Diagram above from American Petroleum Institute. API)
Not Just Hacks but Threats to Our Way of Life
Utilities and supply chains are under siege by both cybercrime opportunists and state sponsored hackers. December 2020- US Department of Energy (US DOE) reports a serious cyber-breach. February 2020- Reading Municipal Light Department (RMLD) reports ransomware. Next, an international lesson: February 2021 Electrobras and Copel, Brazil state owned utilities are hacked. The hack causes the Brazilian utility to suspend “some of its systems” for its Eletronuclear subsidiary. The subsidiary runs two nuclear power plants. Yep, nuclear. This brings us back to oil and gas and how supply disruption can be a significant threat to the American way of life.
Security and Compliance Protects Vital Elements
HIPAA protects the medical us, PCI DSS protects the financial us and SOX protects against the fraud that impacts us. Along with oil in the “US Critical” Energy sector, is electricity. The North American Electric Reliability Corp (NERC) is the electrical grid’s regulatory authority. NERC operates under CIP (Critical Infrastructure Protection) a set of requirements designed to secure the assets required for operating North America’s bulk electric system. Their policies include physical, system and cyber security, access security, recovery and additional elements common to other compliance bodies. Perhaps most importantly in today’s cybercrime environment, NERC CIP includes requirements for regular personnel Cyber awareness and Security training. According to the Wall St Journal and Tobias Whitney VP at Fortress Information Security, “there is no such regulatory body enforcing standards for oil-and-gas companies.”
So, What Now?
Having regulatory bodies and rules doesn’t automatically prevent or fix cybercrime, but they do provide experience based, best in class security guidelines for all companies operating in this critical area. According to the American Petroleum Institute “oil-and-gas companies largely adhere to security recommendations from the National Institute of Standards and Technology.” While the debate moves forward on overall cyber security preparedness for oil and gas (including President Biden recently announcing “We launched a new public private initiative in April, began the 100-day sprint to improve cyber security in the electric sector, and we’ll follow that with similar initiatives in natural gas pipelines, water and other sectors”) here’s some important information about safeguarding your networks:
With ransomware costs estimated to approach nearly $20B in 2021, it’s important for your business to implement the highest level of resilience possible against this evolving disaster. If you are looking for more help increasing your ransomware resilience, Otava can help. Our Veeam Availability Suite offers ransomware protection, powered by Veeam. Get seven-day backup protection that leverages Veeam Insider Protection, ensuring your data remains intact even if a malicious third party remotely wipes your backup data. Start with a free 30 day trial or contact us to learn more.
Additional Resources
Ransomware and Risk Mitigation webinar replay
Listen to the on-demand webinar to learn how organizations can mitigate and protect themselves against ransomware and other malware attacks.
What are the top sources of ransomware infection?
What is ransomware and how do you protect against it?
Video: Ransomware preparedness with Otava, Veeam and MSPs: Our panel covered many topics in a roundtable-style discussion, starting first by reviewing the main strains of ransomware prevalent in the industry today, and what they’re seeing in terms of risk mitigation.