Call Us (877) 740-5028
SecurityMetrics, a merchant data security and compliance company out of Utah, published a report late in 2012 giving information about unencrypted payment card data storage.
Their report was the product of 2,700 payment card discovery scans of merchants varying in size, and the results were pretty shocking. About 71% of merchants had unencrypted payment card data on their business network, adding up to over 315,000 payment cards.
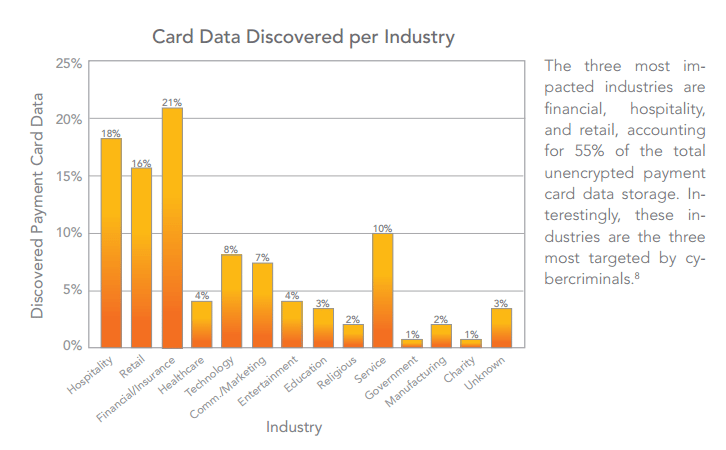
Even more worrisome was the division of industries responsible for the unencrypted data. 21% of that data was under the care of financial and insurance agencies. They were followed closely behind by the hospitality (18%) and retail (16%) industries.
PCI compliance necessitates the encryption of data across open, public networks. However, for stored cardholder data at rest, encryption is not necessary for compliance. Part of this 71% might be using methods other than encryption (truncating data, hashing, or masking are both acceptable given standard 3.4 of PCI requirements) for any stored cardholder data.
In the face of financial industries in the middle of regular DDoS attacks and having some pretty notable breaches in 2012, security needs to be a top concern in 2013, and encryption is one of the best methods for keeping that cardholder data safe.
PCI DSS is all about assessing the risks within a banking or e-commerce business and working to stop those weaknesses from becoming breaches. It’s more than just getting everything done on a specific list. Thus, even without encryption being mandatory, it’s a good idea for keeping client data secure, and can help save the astronomical costs that a breach causes a company.
Related Links:
PCI & HIPAA Data Breaches of 2012: Lessons Learned
Mobile POS & PCI Compliance
Addressing the Top IT Security Issues of 2012
 Looking for more information on PCI hosting requirements, recommendations, and the foundation of a secure PCI compliant data center?
Looking for more information on PCI hosting requirements, recommendations, and the foundation of a secure PCI compliant data center?
Download our PCI Compliant Hosting white paper now for a complete guide to PCI hosting with IT vendors.
Still have questions? Contact us or chat with us now. Find out more about our fully compliant, PCI hosting solutions, or submit a quote request for your project today.
SecurityMetrics, a merchant data security and compliance company out of Utah, published a report late in 2012 giving information about unencrypted payment card data storage.
Their report was the product of 2,700 payment card discovery scans of merchants varying in size, and the results were pretty shocking. About 71% of merchants had unencrypted payment card data on their business network, adding up to over 315,000 payment cards.

Even more worrisome was the division of industries responsible for the unencrypted data. 21% of that data was under the care of financial and insurance agencies. They were followed closely behind by the hospitality (18%) and retail (16%) industries.
PCI compliance necessitates the encryption of data across open, public networks. However, for stored cardholder data at rest, encryption is not necessary for compliance. Part of this 71% might be using methods other than encryption (truncating data, hashing, or masking are both acceptable given standard 3.4 of PCI requirements) for any stored cardholder data.
In the face of financial industries in the middle of regular DDoS attacks and having some pretty notable breaches in 2012, security needs to be a top concern in 2013, and encryption is one of the best methods for keeping that cardholder data safe.
PCI DSS is all about assessing the risks within a banking or e-commerce business and working to stop those weaknesses from becoming breaches. It’s more than just getting everything done on a specific list. Thus, even without encryption being mandatory, it’s a good idea for keeping client data secure, and can help save the astronomical costs that a breach causes a company.
Related Links:
PCI & HIPAA Data Breaches of 2012: Lessons Learned
Mobile POS & PCI Compliance
Addressing the Top IT Security Issues of 2012
 Looking for more information on PCI hosting requirements, recommendations, and the foundation of a secure PCI compliant data center?
Looking for more information on PCI hosting requirements, recommendations, and the foundation of a secure PCI compliant data center?
Download our PCI Compliant Hosting white paper now for a complete guide to PCI hosting with IT vendors.
Still have questions? Contact us or chat with us now. Find out more about our fully compliant, PCI hosting solutions, or submit a quote request for your project today.